Contents
- Militant Networks
- Forced Migration
- Rhetorical Influence of Violent Groups
- Social Media Information Networks
- Readiness and Stochastic Risk Assessment
- Energy and Readiness
- Neural Correlates of Cooperation and Competition
Militant Networks
Violent non-state actors train together, share information, trade together, and conduct attacks together. They also fight as they compete over scarce resources and supporters, and when they cannot commit to cooperation. Cooperation can benefit groups greatly, but competitive pressures and limited resources make trust and cooperation costly. The balance between cooperation and competition leads to dynamic cooperation networks. My dissertation research explores these militant networks: tradeoffs that violent non-state actors make when aligning with others, the consequences of those tradeoffs, and the ways in which a group’s position in a global network affects their vulnerabilities and behavior. I explore these tradeoffs through several research prongs, each contained in separate dissertation papers.
-
-
- How do violent groups learn their violent tactics? How do violent tactics diffuse across networks of partners?
Adopting new violent tactics is risky because failure compromises a group’s operatives and reputation. Sharing operational information necessary for success is also risky, because it risks losing information to security operatives. Groups compensate for these risks by sharing with and learning from trusted partners. This means that network structures mediate the flow of technical knowledge through violent organizations.
Working paper available upon request. - How does a militant group’s network of partners constrain or benefit that group? Do different patterns of partnerships have different effects?
I examine the ways in which groups are constrained and enabled by their network of partners. The structure of a network shapes the ways in which goods and vulnerabilities flow across a network. For example, redundant ties may be inefficient from an information flow standpoint, but may also provide robustness to a trade network at risk of disruption. It follows, then, that different network topologies are more suited to certain tasks, and that groups constrained by certain network topologies may have different vulnerabilities and different strengths than groups constrained by other topologies. I find that more centralized networks tend to be more efficient, facilitating the sharing of information, capacity for violence, and group survival. Moreover, well-connected groups in centralized networks have greater capacity, survival, and learning, with each new partner they have, while well-connected groups in decentralized networks have lower capacity, are less likely to survive, and adopt fewer tactics.
Working paper available on upon request - How do transnational groups decide who to support in local conflicts?
How do transregional groups (such as al Qaeda) choose their local partners, given many options? Which civil wars, and which rebel groups within civil wars, will contribute to a global threat? When do local groups accept sponsorship and when do they refuse? I argue that despite principal agent problems, transregional groups prefer strong local partners, but strong local partners generally do not need sponsorship and prefer autonomy. Partnership is only possible when strong local groups lose access to a critical resource.
Working paper available upon request. - How do groups choose their partners?
Groups will select a portfolio of partnerships that maximizes their net gains from cooperation and minimizes their net risks. I theorize about two different alliance formation strategies: a symmetric strategy and an asymmetric strategy. Because an individual group’s choices are not made independent of the choices made by other groups, I will model these strategies using a computational network model, and compare the resultant network to extant militant group networks.
- How do violent groups learn their violent tactics? How do violent tactics diffuse across networks of partners?
-
Forced Migration
With the Singh Lab at Georgetown’s Massive Data Institute.
As part of an effort to create a migration early warning system, we are identifying predictive signals from online media and social media sources. Knowing when migrants are likely to flee catastrophes of different types, and where they are likely to go, will help us to more efficiently prepare and deliver aid. This wealth of data also provides opportunities for more micro-level hypothesis testing on forced migration to help us understand and alleviate root causes.
As a first step, we are examining migrant flows in Iraq as a response to ISIS related violence.
Rhetorical Influence of Violent Groups
With the Singh Lab at Georgetown’s Massive Data Institute.
Using official statements from ISIS and Al Qaeda, and social media posts from potential sympathizers, I seek to trace the influence of ISIS and al Qaeda both on one another, as well as on far right Islamists generally. I will examine influence over time, and how it is affected by major events and territorial change. This project is in the data collection phase, but will soon move to topic modeling of collected text.
Social Media Information Networks
With the Singh Lab at Georgetown’s Massive Data Institute.
Using twitter data from authorities on parenting, and their social networks, we are examining the flow of information on Twitter and the ways in which these networks interact. Do they cluster by topic? How is information processed and distributed among followers and their networks? This research contributes to a broader project on understanding parental behavior and how social media signals relate to survey data. It will also help us to understand how the flow of information on Twitter differs among consumers and authorities.
Readiness and Stochastic Risk Assessment
Conducted with the Institute for Defense Analyses.
Click here for the latest SARA report

The SARA model is a tool for assessing force structures and force readiness policies under uncertainty over the future threat environment. As one of the lead developers for the model, I built a demand model to use user expectations about the future to simulate random futures and generate force requirements. I also contributed to and built force generation models to meet these uncertain demands, and produced various risk measures. 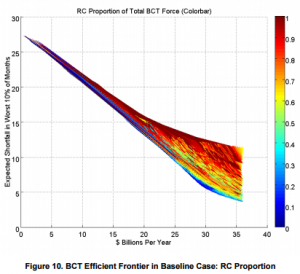 This involved developing an understanding of current and potential force management policies and constraints, and building a model to meet department needs.
This involved developing an understanding of current and potential force management policies and constraints, and building a model to meet department needs.
Energy and Readiness
Conducted wit the Institute for Defense Analyses
Click here for the latest report
Fuel prices are budgeted and appropriated roughly two years in advance, but in recent years, fuel prices have been highly volatile. If fuel prices increase substantially, then funds may be unavailable for pilots to fly, for ships to steam, or for units to drive, which could impact training. What is the effect of an unexpected fuel price increase on readiness? What systems are in place to handle these effects, and is the department facing a potentially serious readiness problem?
Using historical data, and conducting interviews with offices across the Navy, Air Force, and Army, we found no effect of fuel price increases. Reliable systems are in place to handle fuel funding shortfalls. That being said, fuel price increases have the potential to exacerbate already strained budgets when other stressors are present.
Neural Correlates of Cooperation and Competition
 Understanding innate tendencies in cooperation and competition can help us to understand human behavior at a more macro level. Understanding the impact of threat response on cooperative behavior has direct implications for understanding how populations respond to violent tactics, or how leaders respond to threats. A pilot study focused on one aspect of this question: distinguishing between sensitivity to fairness and norms violations, and emotional mechanisms driving social decision bias.
Understanding innate tendencies in cooperation and competition can help us to understand human behavior at a more macro level. Understanding the impact of threat response on cooperative behavior has direct implications for understanding how populations respond to violent tactics, or how leaders respond to threats. A pilot study focused on one aspect of this question: distinguishing between sensitivity to fairness and norms violations, and emotional mechanisms driving social decision bias.
Specifically, what is the effect of emotion on bias during social-decision making in the Ultimatum Game paradigm. Preliminary evidence suggests that negative emotional triggers reduce generosity, and that this behavioral effect may be driven by the insula. Moreover, ungenerous behavior does not require suppression of reward systems after negative emotional triggers.

